Install Strongswan on Amazon Linux 2023 ARM64
這個問題困擾我很久了,Amazon Linux 2023 ARM64 的repo 中軟體太過稀有,以至於很多的軟體都要從Redhat9 的binary 去獲取。
為什麼是ARM64?感覺是個趨勢吧,畢竟是這麼“節儉”的公司,不會亂花錢去做到目前的Graviton 4。
但問題是,官方並沒有明確Amazon Linux 2023 對應到哪一個版本的Fedora 或者RHEL,這就有點玄學的意思,自己試?我試了幾個版本,失敗。
直接從source code 來compile 算了。
dnf install gcc make openssl-devel -y
mkdir src && cd src
wget https://download.strongswan.org/strongswan-6.0.0.tar.gz
tar zxf strongswan-6.0.0.tar.gz && cd strongswan-6.0.0
./configure --prefix=/usr/local/strongswan --enable-libipsec --enable-stroke && make && make install
sudo tee /etc/systemd/system/strongswan.service > /dev/null <<EOL
[Unit]
Description=strongSwan IPsec IKEv1/IKEv2 daemon
After=network.target
[Service]
ExecStart=/usr/local/strongswan/sbin/ipsec start --nofork
ExecStop=/usr/local/strongswan/sbin/ipsec stop
Restart=on-failure
[Install]
WantedBy=multi-user.target
EOL寫入幾個微小的配置檔。
sudo tee /usr/local/strongswan/etc/ipsec.secrets > /dev/null <<EOL
2100:ab16:796:5a00:bg29:6r8d:4dca:b02a someone@aws.net : PSK "86f6g7da3316a95b0f4e6416f4f0b15c44083a8b4c2da0dee8ac"
EOL
sudo tee /usr/local/strongswan/etc/ipsec.conf > /dev/null <<EOL
config setup
uniqueids=never
charondebug="cfg 2, dmn 2, ike 3, net 2"
conn Someone2AWS-v6
authby=secret
left=2100:ab16:796:5a00:bg29:6r8d:4dca:b02a
leftid=2100:ab16:796:5a00:bg29:6r8d:4dca:b02a
leftsubnet=10.4.0.0/16
right=2406:520:88:5cb::1
#right=host.domain.org
rightid=someone@aws.net
rightsubnet=10.1.3.0/24
ike=aes128gcm128-sha256-modp2048!
esp=aes128gcm128-modp2048!
keyingtries=0
ikelifetime=8h
lifetime=1h
auto=start
EOL嘗試啟動
systemctl stop strongswan
systemctl disable strongswan
systemctl daemon-reload
systemctl enable strongswan
systemctl restart strongswan
systemctl status strongswan把ipsec command link 一下
ln -s /usr/local/strongswan/sbin/ipsec /usr/sbin/ipsec
ipsec status查看一下log 是否正常
journalctl -u strongswan --since -1min還需要對防火牆進行一點點改動,打開相應的port 和forward
dnf install firewalld -y
systemctl enable firewalld
systemctl start firewalld
firewall-cmd --zone=public --add-masquerade --permanent
firewall-cmd --zone=public --add-service=ipsec --permanent
firewall-cmd --zone=public --add-service=ssh --permanent
firewall-cmd --permanent --zone=public --add-interface=ens5
firewall-cmd --reload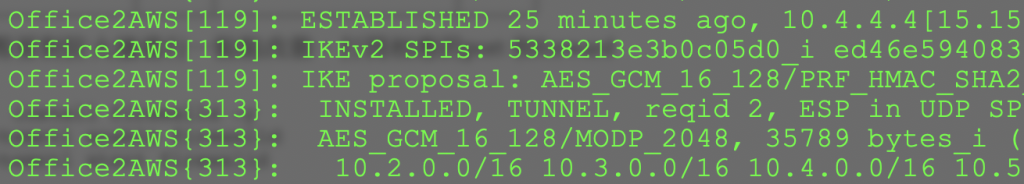
Update 20250429
cd src
curl -O https://download.strongswan.org/strongswan-6.0.1.tar.gz
tar zxf strongswan-6.0.1.tar.gz
cd strongswan-6.0.1
dnf install systemd-devel
./configure --enable-systemd && make && make install
rm /etc/systemd/system/strongswan.service
sudo tee /etc/systemd/system/strongswan.service > /dev/null <<EOL
[Unit]
Description=strongSwan IPsec IKEv1/IKEv2 daemon using swanctl
After=network-online.target
Documentation=man:charon-systemd(8) man:swanctl(8)
[Service]
Type=notify
ExecStart=/usr/local/sbin/charon-systemd
ExecStartPost=/usr/local/sbin/swanctl --load-all
ExecReload=/usr/local/sbin/swanctl --reload
Restart=on-abnormal
[Install]
WantedBy=multi-user.target
EOL是時候拋棄ipsec command了,啟用systemd 和swanctl
一個使用swanctl 的conf
connections {
AWS2BuyVM {
local_addrs = 2605:6600:10:e95:62cb:d245:1888:eeee
local {
id = 2605:6600:10:e95:62cb:d245:1888:eeee
auth = psk
}
remote {
auth = psk
id = 2406:da16:7e3:5a00:ca98:6f8d:4cfe:bbbb
}
remote_addrs = 2406:da16:7e3:5a00:ca98:6f8d:4cfe:bbbb
children {
AWS2BuyVM {
local_ts = 10.30.96.0/24
remote_ts = 10.2.0.0/16,10.3.0.0/16,10.4.0.0/16,10.5.0.0/16
esp_proposals = aes128gcm128-modp2048
life_time = 1h
start_action = route
}
}
version = 2
proposals = aes128gcm128-sha256-modp2048
rekey_time = 8h
keyingtries = 0
}
}
secrets {
ike-AWS2BuyVM {
id-local = 2605:6600:10:e95:62cb:d245:1888:eeee
id-remote = 2406:da16:7e3:5a00:ca98:6f8d:4cfe:bbbb
secret = "0000000000000000_r"
}
}查看一下連結的情況:
swanctl --list-sas
BuyVM2AWS: #17, ESTABLISHED, IKEv2, 6e00f87f2e29ab73_i* b801ad6c15b17e01_r
local '2406:da16:7e3:5a00:ca98:6f8d:4cfe:bbbb' @ 2406:da16:7e3:5a00:ca98:6f8d:4cfe:bbbb[4500]
remote '2605:6600:10:e95:62cb:d245:1888:eeee' @ 2605:6600:10:e95:62cb:d245:1888:eeee[4500]
AES_GCM_16-128/PRF_HMAC_SHA2_256/MODP_2048
established 85s ago, rekeying in 26399s
BuyVM2AWS: #7, reqid 5, INSTALLED, TUNNEL, ESP:AES_GCM_16-128
installed 86s ago, rekeying in 2873s, expires in 3515s
in ce702c32, 4620 bytes, 55 packets, 31s ago
out c273aa68, 4872 bytes, 58 packets, 12s ago
local 10.2.0.0/16 10.3.0.0/16 10.4.0.0/16 10.5.0.0/16
remote 10.30.96.0/24




















